A proliferation of cloud computing, the growth of AI and analytics, and cloudification of the network and the edge demands a datacentric approach to business overall and specifically to business data governance, security, and resilience. No one wants to continue building ‘security stacks’ comprised of 100s of tools that are not solving the problem: keeping your data protected no matter what. Think about it. Your business spends way too much time and money analyzing, integrating, testing, rolling out, and tackling the learning curve on the ‘systems’ instead of where that time would generate ROI: working with your most valuable business asset, the data. With the STASH® datacentric solution, data is protected inside and outside of the organization. The security and governance stay with the data. You can take this positive outcome to the bank by way of recaptured time and resources to spend on making your protected valuable data more profitable.
Rapidly accelerating Enterprise vulnerability due to exponential growth of mobile endpoints and IoT devices (50 Billion connected devices now, 80 Billion forecasted by 2025) means the direct or circuitous routes to your data are simply too numerous to defend. This is not something new. Porous perimeters (let’s be real: the DATA is now the perimeter), poor IT hygiene, failure to accept that cloud security responsibility by cloud vendors only extends as far as their clouds, not to what’s IN their clouds, enable exploits that continue to confound. While you’re adding another defensive tool to your stack in a futile attempt to win at data protection whack-a-mole, malicious actors are going about their business. It’s time to win at this ‘us vs. them’ game. Our zero trust, quantum-resistant, agnostic, no integration solution proactively protects
data everywhere.

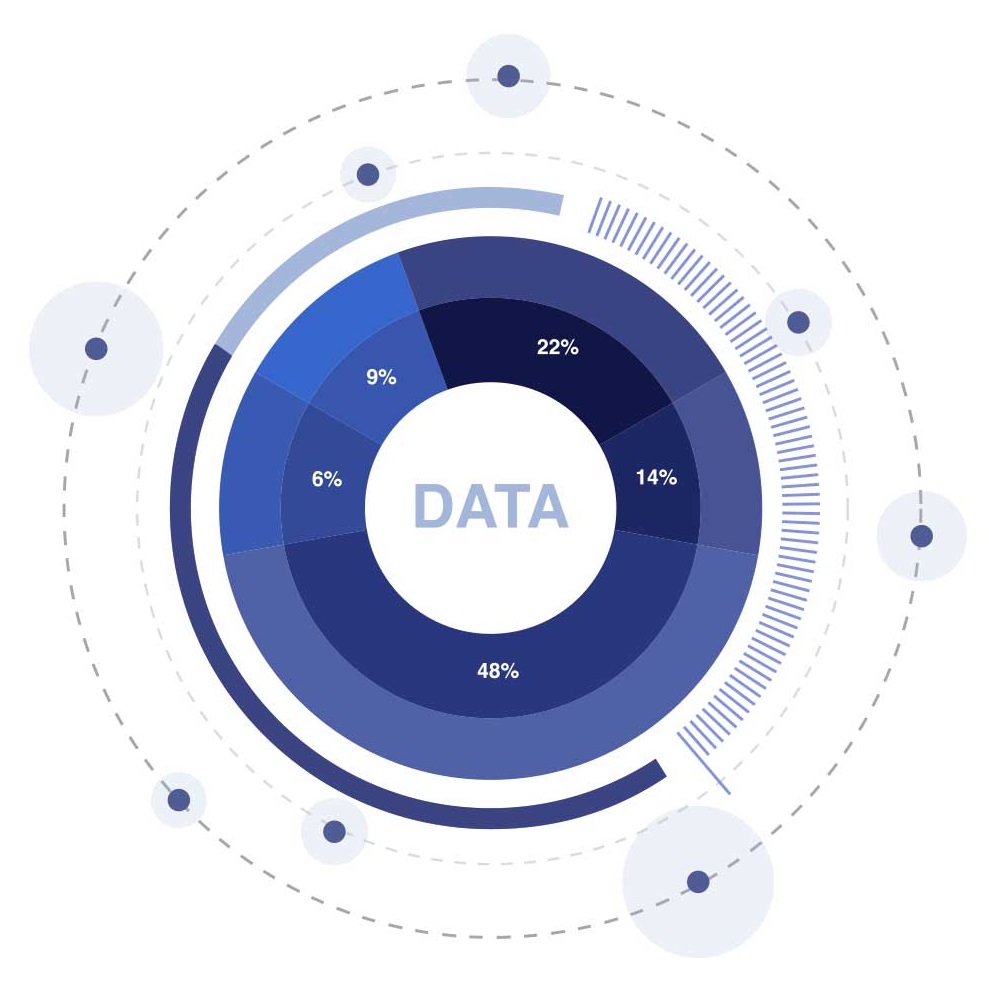
The Cloud currently supports 65% of enterprise workloads, increasing to 80% by 2022. Data shows that though there is tremendous apprehension about moving Business Ops off-site, the train has left the station. More and more Enterprises are using cloud services for complex, mission-critical, and high-risk applications, without understanding that the cloud environment is more vulnerable to data compromise, exploit, loss, harm, and manipulation then imaginable. Here’s something you probably don’t know: Cloud Providers are only responsible for the security of their Clouds–the physical hosts, networks, and data centers. Enterprises are responsible for user identity and access management, data security and handling policies, and security applications. It is a cooperative that is not moving at the pace of business automation, emerging technologies, and ever more sophisticated adversaries. STASH® solves this problem.
Cloud Providers are still operating in a world that includes the concept of a ‘perimeter’. It is true that Cloud security technologies mitigate at least some of the weekend hackers, the ‘bet you I can breach AWS’ thrill seekers, the ‘let me see what I can steal’ insider threats. But the real threats? The nation states, black hats, and freakishly talented 17-year-old technology outliers? They are getting in. STASH® wasn’t built to stop breaches from happening. Because no one, no organization, no technology can do that. What STASH® does is deliver pervasive, persistent, data protection, resulting in resilient, secure, and private data management with controlled access and data governance. Peace-of-mind about data, the lifeblood of your business is not only obtainable, but a given. There is NOTHING like STASH®. Guaranteed. See for yourself.